Anonymity is the top purpose when finding out privateness, and it’s helpful to think about de-anonymization as a sport.
We think about an adversary with some entry to info, and it tries to guess accurately who amongst a set of candidates was chargeable for some occasion within the system. To defend in opposition to the adversary successful, we have to preserve it guessing, which may both imply limiting its entry to info or utilizing randomness to extend the quantity of knowledge it must succeed.
Many readers shall be accustomed to the sport of “Guess Who?”. This sport may very well be described as a turn-based composition of two situations of the extra common sport “twenty questions.” In “twenty questions,” you secretly select a component from a given set, and your opponent tries to guess it accurately by asking you as much as 20 yes-or-no questions. In “Guess Who?” each side take turns taking part in in opposition to one another, and the primary to guess accurately wins. The set of components is mounted in “Guess Who?”, consisting of 24 cartoon characters with numerous distinguishing options, comparable to their hair shade or fashion. Every character has a novel title that unambiguously identifies them.
The solutions to a yes-or-no query could be represented as a bit — zero or one. Twenty bits can specific, in base 2, any entire quantity within the vary 0 to 1,048,575, which is 2²⁰-1. If a set could be completely ordered, every ingredient within the set could also be listed by its numbered place within the order, which uniquely identifies it. So, 20 bits can uniquely handle considered one of simply over 1,000,000 components.
Though 2²⁰ is the utmost variety of components of a set that may very well be uniquely recognized utilizing simply the solutions to twenty yes-or-no questions, in real-world conditions, 20 solutions will usually include much less info than that. For many units and combos of questions, issues will virtually actually not line up completely, and never each query will bisect the candidate components independently of the opposite questions. The solutions to some questions is perhaps biased; some questions’ solutions would possibly correlate with these of different questions.
Suppose that as a substitute of asking one thing like “does your character have glasses?” you all the time ask, “Alphabetically, does your character’s title seem earlier than [median remaining character’s name]?”. This can be a binary search, which can maximize how informative the reply to every query shall be: At each step, the median title partitions the set of remaining characters, and the query eliminates one of many two halves. Repeatedly halving the remaining candidates will slender down the search as shortly as yes-or-no solutions make attainable; solely a logarithmic variety of steps is required, which is way sooner than, say, a linear scan (i.e., checking one after the other: “Is it Alice? No? How about Bob? …”).
Keep in mind that in case you are taking part in to win, the purpose of the sport is to not get probably the most info out of your opponent however to be the primary to guess accurately, and it seems that maximizing the knowledge per reply is definitely not the optimum technique — at the very least when the sport is performed actually. Equally, when utilizing video games to check privateness, one should assume the adversary is rational in accordance with its preferences; it’s pretty simple to by chance optimize for a subtly incorrect end result, for the reason that adversary is taking part in to win.
Lastly, suppose the gamers are not assumed to be sincere. It ought to be obvious that one can cheat with out getting detected; as a substitute of selecting a component of the set at the beginning after which answering actually in response to each query, you possibly can all the time give the reply that would depart the biggest variety of remaining candidates. Adaptively chosen solutions can subsequently decrease the speed at which one’s opponent obtains helpful info to win the sport. On this so-called Byzantine setting, the optimum technique is not the identical as when gamers are sincere. Right here, an opponent’s greatest response can be to stay with binary search, which limits the benefit of taking part in adaptively.
Adaptive “Guess Who?” is fairly boring, much like how tic-tac-toe ought to all the time finish in a draw in the event you’re paying consideration. To be exact, as we’ll see within the subsequent part, there are 4.58 bits of knowledge to extract out of your maximally adversarial opponent, and the principles of the sport can be utilized to drive the opponent to decide to these bits. This implies the primary participant can all the time win after 5 questions. The transcript of solutions in such video games ought to all the time encompass uniformly random bits, as anything would give an edge to 1’s opponent. Sadly, privateness protections utilizing such adaptivity or added randomness are troublesome to construct and perceive, so precise privateness software program is normally considerably more durable to research than these toy examples.
Measuring Anonymity: Shannon Entropy
The info content material of a solution in “Guess Who?” — also referred to as its Shannon entropy — quantifies how stunning it’s to be taught. For instance, in the event you already came upon that your opponent’s character is bald, it received’t shock you to be taught that they don’t have black hair; this reply accommodates no further info. This wasn’t stunning as a result of, earlier than being instructed, you may infer that the chance of getting black hair was zero.
Suppose that two choices stay from the set of candidates; it’s mainly a coin toss, and both of the 2 choices ought to be equally seemingly and, subsequently, equally stunning. Studying that it’s possibility A tells you it isn’t B — equivalently, studying that it’s not B tells you that it have to be A — so just one yes-or-no query, one bit of knowledge, is required to take away all uncertainty.
This worth could be calculated from the chance distribution, which on this binary instance is Bernoulli with p=1/2.
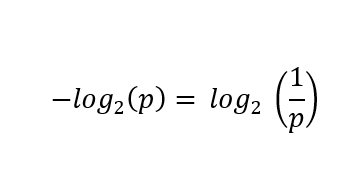
First, compute the negation of the bottom 2 logarithm of the chance of every case, or equivalently invert the chance first and skip the negation:
First, compute the negation of the bottom 2 logarithm of the chance of every case, or equivalently invert the chance first and skip the negation:
In each instances:
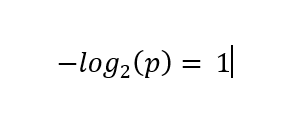
These values are then scaled by multiplying these values by their corresponding possibilities (as a form of weighted common), leading to a contribution of ½ bits for both case. The sum of those phrases, 1 on this case, is the Shannon entropy of the distribution.
This additionally works with greater than two outcomes. In case you begin the sport by asking, “Is it [a random character’s name]?” you’ll probably solely be taught
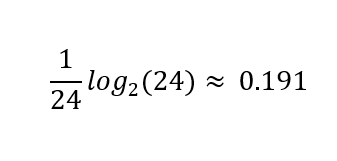
bits of knowledge if the reply was “no.”
At that time log₂(23) ≈ 4.52 bits quantify your remaining uncertainty over the 23 equally seemingly remaining potentialities. Then again, in the event you have been fortunate and guessed accurately, you’ll be taught the complete log₂(24) ≈ 4.58 bits of knowledge, as a result of no uncertainty will stay.
Slightly below 5 bits are wanted to slender all the way down to considered one of 24 characters. Ten bits can establish one in 1,024; 20 bits, round one in 1,000,000.
Shannon entropy is common sufficient to quantify non-uniform distributions, too. Not all names are equally standard, so an fascinating query is, “How a lot entropy is in a reputation“? The linked submit estimates this at roughly 15 bits for U.S. surnames. In accordance with one other paper, first names within the U.S. include roughly 10-11 bits. These estimates indicate an higher sure of 26 bits per full title, however do not forget that a standard title like John Smith will include much less info than an unusual one. (Uniquely addressing the complete U.S. inhabitants requires 29 bits.)
As of writing, the world inhabitants is slowly however absolutely approaching 8.5 billion, or 2³³ individuals. Thirty-three will not be a really massive quantity: What number of bits are in a birthdate? Simply an age? Somebody’s metropolis of residence? An IP handle? A favourite film? A browser’s canvas implementation? A ZIP code? The phrases of their vocabulary, or the idiosyncrasies of their punctuation?
These are tough questions. In contrast to these video games and trendy cryptography, the place secrets and techniques are random and preferentially ephemeral, we will’t randomize, expire or rotate our real-life figuring out attributes.
Moreover, this personally figuring out info usually leaks each by necessity and generally unnecessarily and unintentionally all through our lives. We frequently should belief individuals with whom we work together to not reveal this info, whether or not by sharing it with third events or by chance leaking it. Maybe it’s not in contrast to how we should belief others with our lives, like docs or skilled drivers and pilots. Nonetheless, actually it’s not comparable when it comes to how mandatory it’s to belief as a matter in fact relating to our private knowledge.
An Entropist Perspective on Anonymity
Privateness-enhanced methods enable customers to cover in a crowd. For instance, in the event you observe a connection to your server from a Tor exit node, for all , it’s considered one of probably 1000’s of Tor customers that established that connection. Informally, given some occasion {that a} deanonymization adversary has noticed — maybe by intercepting a message being transmitted between two nodes in a community — a selected consumer’s anonymity set refers back to the set of potential customers to whom that occasion is perhaps attributed.
If the receiver of an nameless message is taken to be the adversary, then their greatest guess from a set of candidate senders is the sender’s anonymity set. If this hypothetical system is totally nameless, then any consumer is equally prone to have despatched the message, aside from the receiver.
Two influential papers that proposed to measure anonymity when it comes to the entropy of the anonymity set have been revealed concurrently: “In the direction of Measuring Anonymity” by Claudia Díaz, Stefaan Seys, Joris Claessens and Bart Preneel, and “In the direction of an Data Theoretic Metric for Anonymity” by Andrei Serjantov and George Danezis. These works generalize from the idea that the adversary can guess the right consumer from an anonymity set no higher than probability, to a mannequin that accounts for nonuniform chance distributions over this set. Each suggest the quantification of anonymity set sizes when it comes to bits of entropy.
When the anonymity set is completely symmetric, solely the uniform distribution is smart, so changing the anonymity set measurement to bits is only a matter of computing a log₂(n) the place n is the dimensions of the set. For instance, 1024 equiprobable components in a set have 10 bits of entropy of their distribution.
When the distribution will not be uniform, the entropy of the distribution decreases. For instance, if both heads or tails is feasible, however there’s a ¼ chance of heads, ¾ of tails, the entire entropy of this distribution is simply
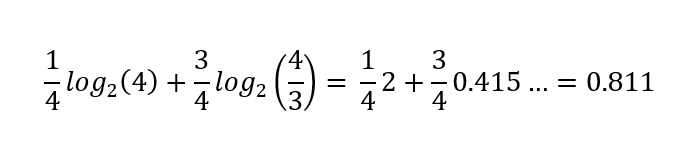
bits as a substitute of a full bit. This quantifies the uncertainty represented in a chance distribution; the result of flipping this bent coin is relatively much less unsure than that of a good coin.
Shannon entropy is a particular case of a whole household of entropy definitions. It characterizes the common info content material in a message (a yes-or-no reply, or extra typically) drawn from a chance distribution over attainable messages. A extra conservative estimate would possibly use min-entropy, which considers solely the best chance ingredient as a substitute of calculating the arithmetic imply, quantifying the worst-case state of affairs. On this submit, we’ll persist with Shannon entropy. For a extra in-depth dialogue and a nuanced interpretation of the entropist perspective, Paul Syverson’s “Why I’m not an Entropist” is a considerate learn.
Anonymity Intersections
In k-anonymity: a mannequin for safeguarding privateness, Latanya Sweeney critiques a few of her prior outcomes as motivation — outcomes which demonstrated re-identification of “anonymized” knowledge. Individually, every attribute in an information set related to an entry, comparable to a date of start, might sound to disclose little or no concerning the topic of that entry. However just like the yes-or-no questions from the sport, solely a logarithmic quantity of knowledge is required; in different phrases, combos of surprisingly small numbers of attributes will usually be enough for re-identification:
For instance, a discovering in that research was that 87% (216 million of 248 million) of the inhabitants in america had reported traits that seemingly made them distinctive based mostly solely on {5-digit ZIP, gender, date of start}. Clearly, knowledge launched containing such details about these people shouldn’t be thought-about nameless.
As a tough estimate, a string of 5 digits would have log₂(10⁵) ≈ 16.6 bits of max entropy, however there are fewer ZIP codes than that, log₂(4.3 x 10⁴) ≈ 15.4 — and needless to say the inhabitants will not be uniformly distributed over ZIP codes, so 13.8 can be a higher estimate. A gender subject would normally include barely greater than 1 bit of knowledge in most circumstances, as a result of even when nonbinary genders are represented, the vast majority of entries shall be male or feminine. That mentioned, entries with nonbinary values would reveal much more than 1 bit concerning the topic of that entry. A date of start can be tough to estimate with out wanting on the distribution of ages.
Ignoring February 29 and assuming uniformly distributed birthdays and 2-digit start yr, the entropy can be log₂(365 x 10²) ≈ 15.1. Once more, a extra sensible estimate is offered, 14.9 bits. Taken collectively, the extra conservative estimates whole roughly 29.7 bits. For comparability, the entropy of a uniform distribution over the U.S. inhabitants on the time is log₂(248 x 10⁶) ≈ 27.9 bits, or log₂(342 x 10⁶) ≈ 28.4 with up-to-date figures.
The next diagram from the paper will most likely look acquainted to anybody who has spent a while studying what an “inside be part of” is in SQL. It illustrates a special instance the place Sweeney linked medical information to the voter registration checklist utilizing the identical fields, figuring out then-Massachusetts Governor William Weld’s particular report in an “anonymized” medical dataset:
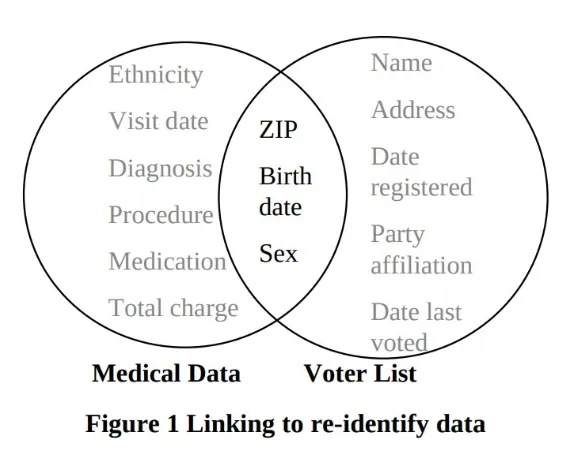
This type of Venn diagram, with two units represented by two overlapping circles and the overlapping half highlighted, sometimes represents an intersection between two units. Units are unordered collections of components, comparable to rows in a database, numbers, or anything that may be mathematically outlined. The intersection of two units is the set of components which are current in each units. So, for instance, throughout the voter registration checklist, we’d speak concerning the subset of all entries whose ZIP code is 12345, and the set of all entries whose start date is January 1, 1970. The intersection of those two subsets is the subset of entries whose ZIP code is 12345 and whose date of start is January 1, 1970. Within the governor’s case, there was only one entry within the subset of entries whose attribute values matched his attributes within the voter registration checklist.
For knowledge units with totally different constructions, there’s a small complication: If we consider them as units of rows, then their intersection would all the time be empty, as a result of the rows would have totally different shapes. When computing the inside be part of of two database tables, solely the values of columns which are current in each tables are in some sense intersected by specifying one thing like JOIN ON a.zip = b.zip AND a.dob = a.dob, or the much less moveable USING(zip, dob) syntax, however these intersecting values are associated to the rows they got here from, so the general construction of linking two knowledge units is a little more concerned.
Notice that Sweeney’s diagram depicts the intersection of the columns of the information units, emphasizing the extra main drawback, which is that attributes included within the “anonymized” knowledge set unintentionally had a non-empty intersection with the attributes of different publicly obtainable knowledge units.
On the utilized facet of the k-anonymity mannequin, the procedures for anonymizing datasets described within the paper have fallen out of favor as a result of some weaknesses found in subsequent work (“Assaults on Deidentification’s Defenses” by Aloni Cohen). That central concept in k-anonymity is to make sure that for each attainable mixture of attributes, there are at the very least ok rows containing each particular mixture within the knowledge, which suggests log₂(ok) further bits of knowledge can be wanted to establish an entry from its congruent ones. The deidentification process recommended for guaranteeing this was the case was to redact or generalize in a data-dependent approach, for instance, drop the day from a date of start, maintaining the yr and month, and even solely the yr, if that’s not sufficient. Cohen’s work exhibits how simple it’s to underestimate the brittleness of privateness, as a result of even discarding info till there’s ok of each mixture, the redaction course of itself leaks details about the statistics of the unredacted knowledge set. Such leaks, even when very refined, won’t solely add up over time, however they are going to sometimes compound. Accounting for privateness loss utilizing bits, that are a logarithmic scale, maybe helps present a greater instinct for the sometimes exponential charge of decay of privateness.
Anonymity in Bitcoin CoinJoins: Intersection Assaults
Of their paper “When the Cookie Meets the Blockchain: Privateness Dangers of Net Funds by way of Cryptocurrencies,” Steven Goldfeder, Harry Kalodner, Dillon Reisman and Arvind Narayanan describe two impartial however associated assaults. Maybe extra importantly, additionally they make a really compelling case for the brittleness of privateness extra broadly, by clearly demonstrating how privateness leaks can compound.
In Bitcoin, a pure definition of an anonymity set for a coin is the set of pockets clusters into which the coin may plausibly be merged. The anonymity set is nontrivial if there’s a couple of candidate cluster, during which case merging can be contingent on acquiring further info. New transactions would possibly introduce uncertainty, necessitating the creation of latest clusters for outputs that may’t be merged into any present cluster (but). Then again, new transactions and out-of-band info can even take away uncertainty and facilitate the merging of clusters. Mostly, if the multi-input heuristic is taken into account legitimate for such a brand new transaction, then the clusters of the enter cash shall be merged. Nonetheless, as we noticed earlier than, many heuristics exist, a few of that are alarmingly correct.
Suppose that Alice obtained some bitcoin right into a pockets below her management. Some might need been withdrawn from an trade (presumably with KYC info). Perhaps a buddy paid her again for lunch. Perhaps she offered her automobile. After making a number of transactions, Alice realizes that her transaction historical past is seen to all and fairly simple to interpret, however quickly she might want to make not only one, however two separate transactions, with stronger privateness assurances than she has been counting on thus far.
After studying a bit about privateness, Alice decides to make use of a pockets that helps CoinJoin. Over a number of CoinJoin transactions, she spends her present cash, acquiring substitute cash that apparently have a non-trivial anonymity set. Earlier than CoinJoining, her pockets was seemingly clusterable. After CoinJoining, every UTXO she now has can’t be assigned to any particular cluster, since different customers’ pockets clusters are additionally implied within the numerous CoinJoin transactions.
The instinct behind CoinJoin privateness is that since a number of inputs belonging to totally different customers are used to create outputs that every one look the identical, nobody output could be linked to a selected enter. That is considerably analogous to a mixnet, the place every CoinJoin transaction is a relay and the “messages” being combined are the cash themselves. This analogy could be very simplistic, there are a lot of issues when implementing CoinJoins that trigger it to interrupt down, however we’ll ignore these nuances on this submit and provides Alice’s chosen CoinJoin pockets the advantage of the doubt and assume that Alice can all the time efficiently spend only one enter into every CoinJoin, and that this leads to excellent mixing of her funds with these of the opposite events to the CoinJoin. Beneath these assumptions, if there are ok equal outputs in a CoinJoin transaction, and ok separate clusters for the inputs, then every output’s anonymity set ought to have log₂(ok) bits of entropy when this transaction is created.
Put up-CoinJoin Clustering
The stage is now set for the primary assault described within the paper. This assault was made attainable by inclusion of third social gathering assets, e.g., a cost processor’s javascript on service provider web sites. Supposing the cost handle used for the transaction is revealed to the third social gathering, that might hyperlink Alice’s net session to her on-chain transaction. The paper is from 2017, so the specifics of web-related leaks are considerably dated by now, however the precept underlying this concern is as related as ever.
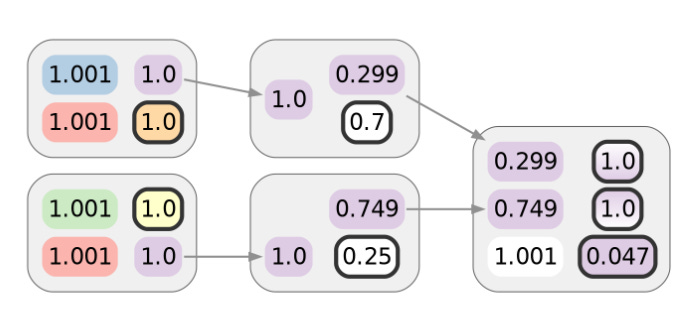
Alice makes use of considered one of her CoinJoin UTXOs to make the primary of these privacy-demanding transactions. Assuming no semantic leaks (comparable to a billing handle associated to a purchase order) or metadata leaks (maybe she broadcasts utilizing Tor), this transaction ought to protect the privateness Alice obtained from the prior CoinJoin transaction. As drawn right here, that might be 1 bit’s price. The colours of inputs or outputs point out the cluster they’re already assigned to. Alice’s cash are in pink, and gradients characterize ambiguity:
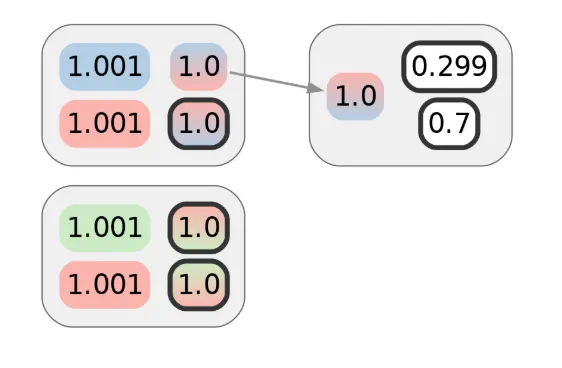
Whereas the primary transaction doesn’t reveal a lot by itself, suppose Alice makes one other transaction. Let’s say it’s with a special service provider, however one which makes use of the identical cost processor as the primary service provider. Naively, it will seem that the next diagram represents the privateness of Alice’s cost transactions, and that the adversary would want 2 bits of further info — 1 for every transaction — to attribute them each to Alice’s cluster:
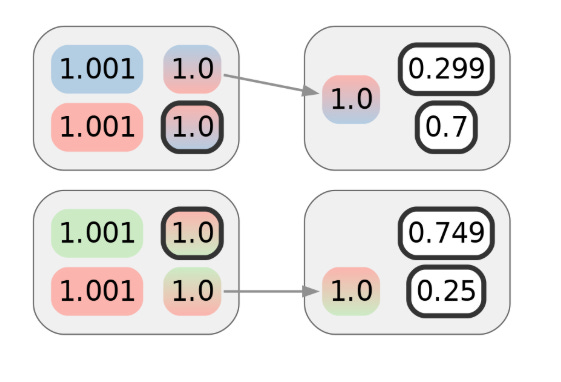
Though Alice intends this to be unlinkable to the primary transaction, she won’t notice her net shopping exercise is being tracked. The paper confirmed that this type of monitoring was not simply attainable however even sensible, and might disclose to a 3rd social gathering that the 2 transactions could be clustered regardless that they don’t seem associated on-chain. Visually, we will characterize this clustering with further colours:
Net monitoring, as mentioned within the paper, is only one of some ways info that facilitates clustering can leak. For instance, web site breaches can lead to buy information being made public, even years after the actual fact. In at the very least one instance, authorized proceedings, that are supposed to guard victims, ended up exposing them to much more hurt by needlessly revealing details about the on-chain transactions of consumers by improper redaction of the transacted quantities. The earlier submit on the historical past of pockets clustering supplies a number of further examples.
Particularly within the context of CoinJoins, a typical approach that this form of linkage may happen is when the change outputs of post-mix cost transactions are subsequently CoinJoined in a way that causes them to be linkable by clustering the inputs. That is also referred to as the poisonous change drawback, which is illustrated within the subsequent diagram. Notice that white doesn’t characterize a single cluster, simply lack of clustering info on this instance.
If the coordinator of the supposedly “trustless” CoinJoin protocols is malicious, then even making an attempt to CoinJoin might hyperlink the transactions, even when this doesn’t grow to be self-evident on-chain. The implications are the identical because the assault described within the paper, besides {that a} CoinJoin coordinator can even faux that some individuals didn’t submit their signatures in time, actively however covertly, or at the very least deniably disrupting rounds to acquire extra clustering info.
Intersection Antecessor Clusters
Sadly for Alice, the story doesn’t finish there. What the paper confirmed subsequent was that given such linking of post-CoinJoin transactions, no matter how this clustering was realized, an intersection assault on the privateness of the CoinJoin transactions themselves additionally turns into attainable.
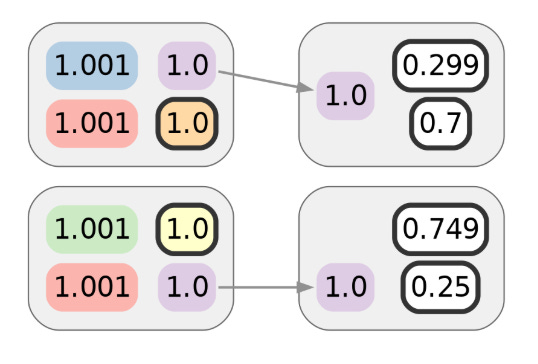
It’s as if the adversary is taking part in “Guess Who?” and is given a cost transaction, then tries to guess the place the funds originated from. Contemplate the set of inputs for every CoinJoin transaction. Each one of many spent cash is assigned to some cluster. Each one of many CoinJoin transactions Alice participated in has an enter that’s linkable to considered one of her clusters. The privateness of such transactions derives from being linked to a lot of in any other case unrelated clusters. Armed with data that post-CoinJoin transactions hyperlink a number of CoinJoin outputs collectively, the adversary can compute the intersection of the units of related clusters. How usually will it’s the case {that a} random particular person consumer participated in each transaction that Alice did? What about a couple of? Not fairly often. And suppose the intersection accommodates a novel cluster, which may usually finally be the case. In that case, the adversary will be capable to hyperlink Alice’s transactions to one another and her pre-CoinJoin transaction historical past, successfully undoing the combo.
Visually, this combines the inferences of earlier diagrams. For every coin within the purple cluster of the final two diagrams, we will intersect the units of colours within the gradients depicted within the diagram earlier than that:

Solely Alice’s pink cluster is within the intersection, in order that the purple cluster could be merged into the pink one. Not solely do Alice’s clusters merge, since this instance solely has two consumer CoinJoin transactions, the remaining clusters may also be merged with their ancestors by technique of elimination, so Alice’s linkable funds would additionally probably deanonymize a hypothetical Bob and Carol on this explicit case:

This means that even when CoinJoins functioned like an ideal combine (which they don’t), inadequate post-mix transaction privateness can moreover undermine the privateness of the prior CoinJoin transactions, and way more quickly than appears intuitive. The graph construction, which connects Bitcoin transactions, accommodates a wealth of knowledge obtainable to a deanonymization adversary.
Privateness issues are sometimes downplayed, maybe as a result of defeatist attitudes in gentle of the challenges of stopping and even controlling privateness leaks. Hopefully consciousness will enhance, and issues will play out like they did in cryptography in earlier a long time — whether or not it’s not delivery weak “export” crypto, or how timing facet channels have been principally ignored at first, however at the moment are broadly understood to be virtually exploitable and implementations that don’t take them under consideration are thought-about insecure. That mentioned, it’ll all the time be more difficult: In cryptography, we have now extra alternatives to restrict the hurt of unintended publicity by preferring ephemeral keys over long-term ones, or at the very least rotating long-term keys periodically. Sadly, the closest analog of rotating keys I can consider in privateness is witness safety applications — a relatively excessive and expensive measure, and much from completely efficient.
For privateness in the actual world, the challenges of CoinJoin privateness stays.
That is an edited model of the article by @not_nothingmuch, posted on Spiral’s Substack June 11.
BM Large Reads are weekly, in-depth articles on some present matter related to Bitcoin and Bitcoiners. If you might have a submission you suppose suits the mannequin, be at liberty to succeed in out at editor[at]bitcoinmagazine.com.








