At Consensus 2026, Cardano’s Charles Hoskinson stated that “customers ought to in all probability by no means have their personal keys,” including that “one thing ought to have the personal keys for the customers.”
He argued that the safe chips already embedded in iPhones, Android telephones, and Samsung units outperform these in Ledger and Trezor units, and that the majority crypto customers already carry higher signing {hardware} of their pockets with out realizing it.
Personal key administration has been a bottleneck to retail adoption since Bitcoin’s earliest days. Customers have bother with their 12- or 24-word seed phrase, normally forgetting it, photographing it, storing it in cloud notes, or shedding it fully.
{Hardware} wallets solved the extraction downside, since a Ledger or Trezor generates and shops keys that by no means depart the machine in plaintext, whereas introducing a friction that mainstream customers have persistently rejected.
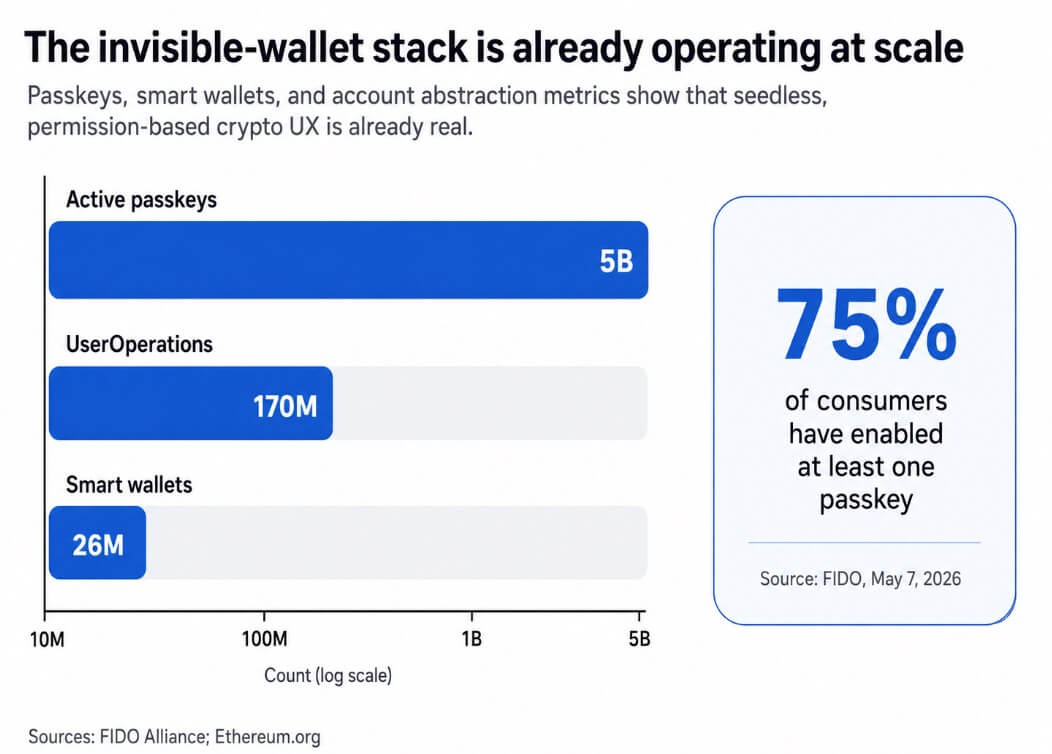
FIDO reported on Could 7 that there at the moment are 5 billion energetic passkeys globally, with 75% of shoppers having enabled at the very least one. Customers already settle for device-bound, biometric-unlocked credentials as a traditional a part of authentication.
Coinbase’s sensible pockets operationalizes this by letting customers onboard with out a restoration phrase, utilizing Apple or Google passkeys, and by making a non-exportable credential certain to safe {hardware}. Face ID or a PIN turns into the one interface the consumer wants.
Hoskinson is appropriate that mainstream telephones include critical safety {hardware}. Apple’s Safe Enclave is a devoted subsystem remoted from the primary processor, and the agency says it protects delicate information even when an attacker compromises the application-processor kernel.
Android’s Keystore system helps hardware-backed keys that may keep non-exportable and bind to a Trusted Execution Surroundings or safe factor, with StrongBox implementations including a devoted CPU and additional isolation necessities.
Samsung’s Knox system supplies hardware-backed key safety by way of TrustZone, with DualDAR including further encryption layers for managed work profile information.
Hoskinson described the Knox work profile as “a separate working system, separate circuits within the {hardware}.”
ModelWhere the important thing livesCan the important thing be extracted?Can malware nonetheless trick signing?How transaction particulars are verifiedBest use caseSeed phrase walletDerived from a 12- or 24-word restoration phrase, usually saved in software program or written down by the userYes, probably — the key may be uncovered by way of dangerous storage, screenshots, cloud backups, phishing, or machine compromiseYes — if the pockets app or machine is compromised, the attacker could trick the consumer or steal the key outrightUsually by way of the pockets app interface on the identical deviceLow-friction onboarding, small balances, customers comfy with guide backupPhone-based hardware-backed walletInside a cellphone’s safe {hardware}, resembling Apple Safe Enclave, Android Keystore/TEE/StrongBox, or Samsung Knox-backed protectionsGenerally no — the important thing can stay non-exportable and certain to machine hardwareYes — the important thing could keep protected, however a compromised app or OS might nonetheless attempt to get the machine to signal one thing maliciousThrough the cellphone UI, biometrics, PIN, and pockets prompts; safety relies upon closely on approval UX and intent verificationEveryday funds, routine self-custody, mainstream customers, seedless/passkey-style onboardingDedicated {hardware} walletInside a separate signing machine resembling Ledger or TrezorGenerally no — keys are designed to remain on the machine and never depart in plaintextMuch more durable, however not not possible — the secret’s higher remoted, although attackers should still attempt to deceive the consumer into approving a nasty transactionOn the pockets’s personal trusted show / safe display, bodily separate from the cellphone or computerLarger balances, long-term storage, customers who need stronger isolation and a cleaner menace mannequin
Devoted wallets maintain a bonus
Telephone-based safe {hardware} and devoted signing units function on completely different menace fashions.Ledger’s safe factor drives a safe display on the machine itself, so customers can confirm transaction particulars even when the linked cellphone or laptop computer is underneath assault.
Trezor’s trusted show reveals the transaction being signed, no matter what the host machine shows. Trezor’s newer Secure 3, Secure 5, and Secure 7 fashions additionally embody safe components, so the critique that {hardware} wallets lack safe silicon is now outdated.
The shortcoming Hoskinson recognized is accessibility, since Ledger and Trezor require a separate machine, a companion app, and a signing stream that interrupts the transaction.
For on a regular basis transaction volumes and routine self-custody, telephones are believable main signers. For bigger balances or customers who need the strongest accessible menace mannequin, devoted units with remoted shows maintain the signing display bodily separate from the compromised machine, guaranteeing that the host’s malware can not attain the show.
The combination of AI into funds provides a layer to the stack. AI brokers want fee authority to be helpful, however granting an agent entry to a grasp personal secret’s one thing most customers wouldn’t knowingly settle for.
The viable structure is bounded delegation, consisting of an agent licensed to spend inside preset limits, throughout a set interval, with out entry to the credential that controls the broader pockets.
Base’s Spend Permissions documentation already frames AI-agent purchases as a core use case for recurring, limited-scope authorizations. Coinbase’s AgentCore Funds integration and AWS’s stablecoin agent fee tooling implement the identical mannequin of brokers transacting underneath price range controls with full audit logs, with out direct private-key entry.
Ethereum’s EIP-4337 has enabled over 26 million sensible wallets and 170 million UserOperations, and Pectra’s EIP-7702 extends programmable pockets conduct to externally owned accounts, enabling batching, fuel sponsorship, restoration logic, and customized controls.
The infrastructure for permission-based, agent-compatible wallets already exists at a significant scale.
Your keys, however you by no means see them
“Not your keys, not your cash” was all the time as a lot a philosophical place as a technical one, and it assumes that customers ought to deal with cryptographic secrets and techniques straight.
But, this place could not survive contact with mass-market distribution. The extra sturdy model of self-custody appears like biometric-based authentication and producing a non-exportable key in safe {hardware}, with out seeing the uncooked key materials.
What the consumer controls are spending caps, session keys, delegated allowances, restoration logic, and human-readable approval flows.
Apple’s safe intent mechanism lets {hardware} bodily affirm consumer intent in a method even root or kernel software program can not spoof. Android Keystore helps per-operation authentication necessities.
These capabilities relocate custody from “can you retain a secret” to “are you able to confirm what you meant to authorize.”
The sharpest limitation in Hoskinson’s framing is {that a} compromised software or working system could also be unable to extract a hardware-backed key whereas nonetheless having the ability to apply it to the machine.
Key non-extractability and transaction safety are separate ensures, and up to date historical past reveals how catastrophically that distinction can play out.
CertiK’s evaluation of the Bybit incident discovered that attackers deceived signers into authorizing a malicious transaction. The assault succeeded even because the personal key by no means left the {hardware}.
Chainalysis reported that impersonation scams grew over 1,400% in 2025, and AI-enabled scams produced 4.5 occasions the returns of conventional ones.
A phone-native self-custody mannequin would cover personal keys from customers and concurrently make transaction intent, approval UX, and spending limits the first safety floor.
Two trajectories
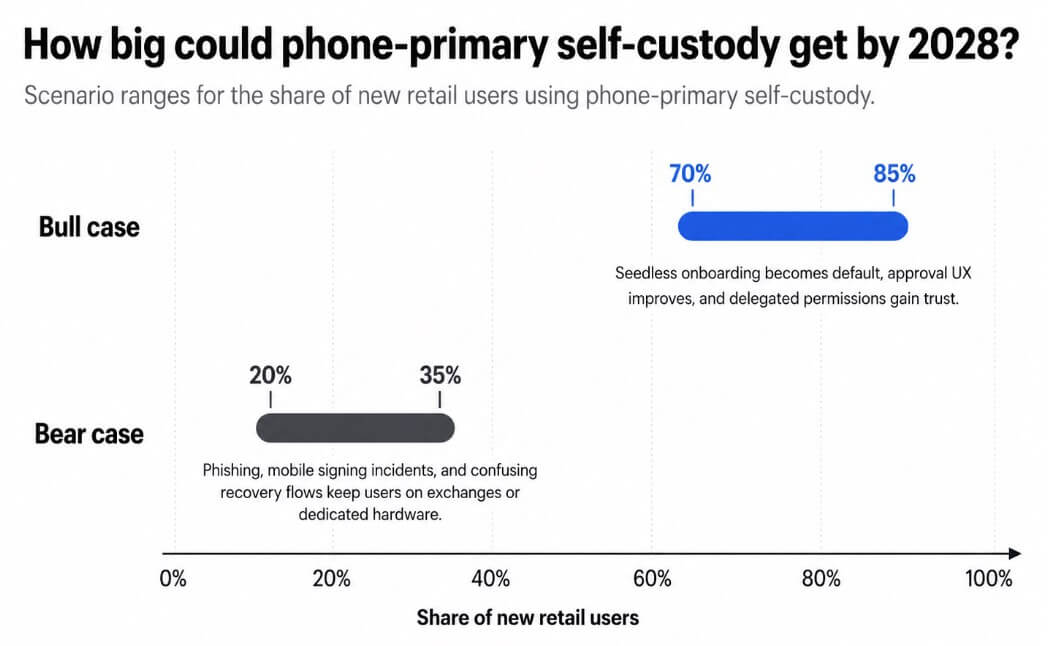
If wallets resolve intent UX properly sufficient to earn client belief by way of standardized spend caps, revocable delegation, and clear approval prompts, phone-primary self-custody might account for 70% to 85% of recent retail customers by 2028.
Seedless onboarding turns into the default, account abstraction strikes from superior function to baseline expectation, and the seed phrase turns into a configuration choice for customers who need it.
If cellular signing incidents, phishing, compromised approval flows, or complicated restoration mechanics proceed to supply high-profile losses, phone-based self-custody stalls at 20% to 35% of the retail market.
Customers who lose funds as a consequence of a cellphone pockets manipulation assault describe it as a hack and return to exchanges.
The uncomfortable subtext in both trajectory is platform dependence. If self-custody strikes into {hardware} embedded inside telephones, then Apple, Google, Samsung, and main pockets SDK suppliers turn into fairly highly effective facilities in crypto’s safety structure.
The mannequin stays non-custodial in a technical sense, however pockets safety relies upon extra on OS APIs, enclave entry insurance policies, and app distribution guidelines.








