A crypto founder had his laptop computer compromised when he joined what gave the impression to be a Microsoft Groups name with Pierre Kaklamanos, a Cardano Basis contact he had spoken with earlier than.
When “Pierre” reached out about Atrium and despatched a Groups invite, nothing seemed misplaced. On the decision, the face and voice matched what he remembered, and two different obvious basis members had been current.
When the decision lagged and dropped him, a immediate instructed him his Groups software program was old-fashioned and wanted reinstalling by Terminal. He ran the command, then shut the laptop computer off as a result of the battery was dying, which restricted the harm on reflection.
He describes himself as “fairly technically savvy,” which is a part of the purpose that the assault labored as a result of the context felt legit.
Social engineers have at all times relied on familiarity, and executing that at scale as soon as required both a compromised account or weeks of text-based rapport-building.
The video name was the authentication layer, the factor victims discovered to belief, and replicating it’s now inside attain.
Pretend replace
Microsoft documented campaigns in February and March 2026 by which malicious information masqueraded as office apps, corresponding to msteams.exe and zoomworkspace.clientsetup.exe, with phishing lures that mimicked legit Groups and Zoom assembly workflows.
In a separate warning, Microsoft described “ClickFix”-style prompts focusing on macOS customers, instructing them to stick instructions into Terminal and focusing on browser passwords, crypto wallets, cloud credentials, and developer keys.
The faux Groups replace suits each patterns concurrently.
Google Cloud’s Mandiant unit described a crypto-focused intrusion constructed on the identical construction. A compromised Telegram account, a spoofed Zoom assembly, what witnesses described as a deepfake-style government video, and troubleshooting instructions that launched the an infection.
Mandiant stated it couldn’t independently confirm which AI mannequin, if any, generated the video, however confirmed the group used faux conferences and AI instruments throughout social engineering.
On Apr. 24, the true Pierre Kaklamanos posted on X saying his Telegram had been hacked and that somebody was impersonating him, together with “a number of different folks within the business this week.”
He instructed followers to keep away from clicking hyperlinks or reserving conferences by the account and to confirm contact by LinkedIn direct messages.
By then, the founder had already messaged the account suggesting they change to Google Meet. Whoever managed Pierre’s Telegram account replied that he had gotten busy and requested to reschedule, with the attacker nonetheless managing the persona as soon as the decision ended.
That trade turns the incident from an remoted embarrassment right into a stay marketing campaign sign that the tactic is energetic, the account compromise is the entry level, and the connection historical past is the weapon.
StageWhat the sufferer sawWhy it seemed legitimateWhat the attacker was seemingly attempting to achieveInitial outreach“Pierre” reached out about Atrium and urged a callThe sufferer had spoken with Pierre earlier than, together with on videoReopen an current belief relationship as a substitute of ranging from a chilly approachMeeting setupA Microsoft Groups invite for the subsequent dayTeams is a traditional enterprise workflow and the subject was plausibleMove the goal right into a managed atmosphere that felt routineLive callFamiliar face, acquainted voice, plus two different obvious Cardano Basis membersThe social context matched the sufferer’s reminiscence of prior interactionsLower suspicion and make the decision itself really feel like verificationCall disruptionLagging, instability, then getting kicked outTechnical glitches are widespread in video callsCreate frustration and arrange the faux “repair” as a traditional troubleshooting stepFake replace promptA message saying Groups was old-fashioned and wanted reinstalling by TerminalSoftware replace prompts are acquainted, and the person hardly ever used TeamsGet the sufferer to execute a malicious command directlyCommand executionThe sufferer ran the command, then shut down the laptop computer as a result of the battery was dyingThe workflow nonetheless felt like a routine app repair at that momentLaunch the an infection chain and achieve entry to credentials or system dataPost-call follow-upThe sufferer urged switching to Google Meet; the attacker stated he obtained busy and requested to rescheduleThe persona continued behaving like an actual contact after the failed attemptKeep the connection alive for one more try and keep away from instant suspicion
Why generative media adjustments the risk floor
The founder stated he now believes the decision might have concerned AI-generated or manipulated video. Forensic affirmation of the instruments is missing, and the OpenAI connection right here is ruled by its personal security documentation.
OpenAI launched its 4o picture technology mannequin on Mar. 25, describing it as able to “exact, correct, photorealistic outputs,” and launched the ChatGPT Pictures 2.0 System Card on Apr. 21.
The agency said that the mannequin’s “heightened realism” may, absent safeguards, allow extra convincing deepfakes of actual folks, locations, or occasions. One of many main AI labs has now placed on file that its personal picture mannequin raises the ceiling on what a convincing faux can seem like.
The World Financial Discussion board stated in January 2026 that generative AI lowers the barrier to phishing whereas elevating its credibility, by sensible deepfake audio and video that may evade each detection programs and human scrutiny.
INTERPOL declared monetary fraud one of many world’s most extreme and quickly evolving transnational crimes in March 2026, figuring out deepfake movies, audio, and chatbots as instruments that make impersonation of trusted folks simpler to hold out at scale.
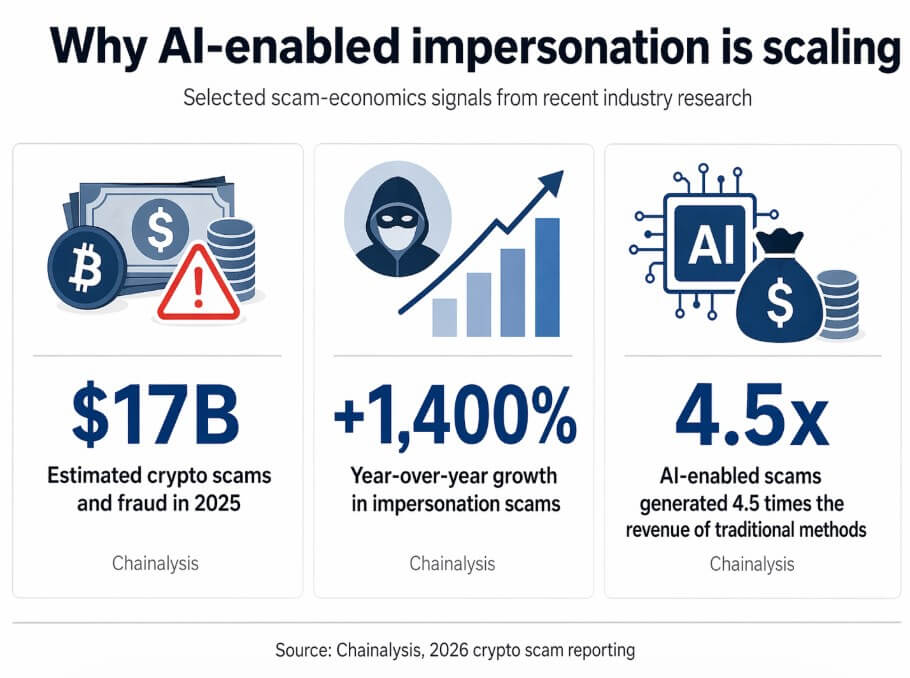
Chainalysis estimated that crypto scams and fraud reached $17 billion in 2025, with impersonation scams up 1,400% 12 months over 12 months and AI-enabled scams producing 4.5 instances as a lot income as conventional strategies.
Crypto attracts this class of assault as a result of it combines high-value targets, quick settlement rails, and a casual communications tradition by which Telegram introductions and advert hoc video calls between founders are routine.
Mandiant documented that the group behind the crypto Zoom intrusion focused software program companies, builders, enterprise companies, and executives throughout funds, brokerage, staking, and pockets infrastructure.
Mandiant famous that the sufferer’s information might be used to seed future social engineering, with every compromise producing materials for the subsequent.
Two paths ahead
Zoom introduced on Apr. 17 a partnership so as to add real-time human verification to conferences, a “Verified Human” badge, and a “Deep Face Ready Room,” treating participant authenticity as a product downside.
Gartner predicts that by 2027, 50% of enterprises will spend money on disinformation-security merchandise or TrustOps methods, up from lower than 5% at present.
Within the bull case, that buildout reaches essential mass rapidly sufficient that attackers should defeat a number of unbiased belief layers to finish a conversion, and the economics of impersonation campaigns deteriorate.
Within the bear case, the timeline compresses earlier than defenses do. Gartner warned that AI brokers might halve the time required to use account takeovers by 2027, narrowing the window for human hesitation or safety crew intervention.
Deloitte estimated that generative AI-enabled fraud losses within the US alone may climb from roughly $12 billion in 2023 to $40 billion by 2027.
ScenarioWhat changesWhat stays vulnerableImplication for crypto firmsBull caseVerification instruments unfold rapidly: human-verification badges, liveness checks, stronger inner belief rails, and extra formal approval workflowsInformal founder-to-founder chats, legacy messaging habits, and advert hoc scheduling nonetheless create openingsAttackers face extra friction and decrease conversion charges as a result of they have to defeat a number of belief layers as a substitute of oneBear caseAI-generated impersonation improves quicker than defenses are adopted; faux conferences and faux troubleshooting turn into commonplace playbooksPublic-facing executives, Telegram-based outreach, video-first verification habits, and employees below time pressureRelationship hijacking turns into routine, and every compromise creates materials for the subsequent scamWhat success appears to be like likeSensitive requests get verified throughout separate channels, with recognized numbers, shared passphrases, {hardware} keys, or pre-agreed inner systemsSocial stress, urgency, and belief in acquainted faces and voices can’t be totally removedFirms cut back the prospect that one spoofed name can lead on to compromiseWhat failure appears to be like likeTeams depend on the decision itself as proof of id, at the same time as deepfake and impersonation instruments improveVideo stays persuasive even when it’s not dependable as authenticationCrypto organizations turn into simpler to focus on as a result of executives are each high-value victims and reusable lure belongings
Each public-facing crypto government turns into each a goal and a lure asset, a supply of voice recordings, video clips, and relationship graphs that attackers can deploy in opposition to the subsequent sufferer.
Zoom is constructing liveness checks into conferences, Microsoft is documenting assault chains that impersonate its personal software program, and the FBI has warned that malicious actors are already utilizing AI-generated voice and textual content to impersonate trusted contacts, advising in opposition to assuming a message is genuine as a result of it seems to come back from a recognized particular person.
Verification now requires unbiased rails, corresponding to a recognized cellphone quantity, a {hardware} key, a shared passphrase established earlier than any assembly, or a pre-agreed inner channel that no attacker has accessed.








