Cybercriminals who goal crypto should not working on a set schedule. They transfer when the cash strikes.
That was the important thing message from Kraken’s chief safety officer, Nick Percoco, who informed reporters that hacking exercise within the crypto house tends to spike throughout bull markets, main product launches, and durations of fast progress — not due to the calendar, however as a result of these are the moments when probably the most worth is concentrated in a single place.
“Vulnerabilities could be exploited in any market surroundings,” Percoco mentioned, warning that safety in crypto needs to be handled as an ongoing effort, not a seasonal one.
His feedback got here as new information confirmed a notable drop in crypto theft throughout the first three months of 2026. Based on DefiLlama, hackers pulled $168 million from 34 decentralized finance protocols between January and March — a steep fall from the $1.58 billion stolen throughout the identical interval final yr.
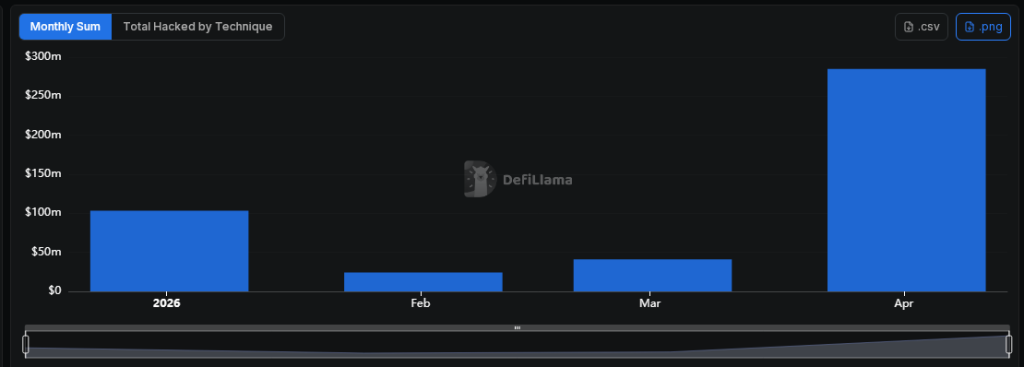
DefiLlama reviews that stolen funds in Q1 2026 have been down from the earlier yr.
Non-public Keys And Good Contracts Stay Weak Spots
That prior-year determine, nonetheless, was closely skewed by a single incident: the $1.4 billion Bybit breach, which accounted for almost all the Q1 2025 complete. Strip that out and the comparability seems to be much less dramatic.
Nonetheless, the losses in early 2026 have been removed from small. The largest hit got here in January, when portfolio administration platform Step Finance misplaced $40 million after attackers compromised its non-public keys.
Days later, on Jan. 8, decentralized protocol Truebit was drained of $26.4 million value of ether via a sensible contract manipulation. A 3rd main incident struck stablecoin issuer Resolv Labs in late March, additionally via a personal key compromise — the identical methodology used within the Step Finance assault.
Non-public key failures and code exploits are two very completely different issues, however each maintain showing within the information. One is a human and operational subject. The opposite is a code subject. Neither has been solved.
North Korea-Linked Teams Stay A Persistent Concern
Knowledge exhibits that 34 separate DeFi protocols have been hit throughout the quarter. The assaults have been unfold throughout the interval, with January bearing the heaviest losses.
Percoco described the menace pool as a mixture of extremely coordinated teams, organized felony networks, and opportunistic people scanning for weak factors in sensible contracts and user-facing techniques.
North Korea-linked actors have been flagged repeatedly in reference to main crypto thefts. Suspected associates of that community have been linked to an assault on decentralized change Drift Protocol, which misplaced an estimated $285 million to a personal key leak.
Featured picture from Unsplash, chart from TradingView

Editorial Course of for bitcoinist is centered on delivering completely researched, correct, and unbiased content material. We uphold strict sourcing requirements, and every web page undergoes diligent assessment by our crew of high expertise consultants and seasoned editors. This course of ensures the integrity, relevance, and worth of our content material for our readers.







